Recently, Omroep Brabant worte an article about Cyber4Z concerning a cyberattack on a dental organization. This article was written by Dit artikel is geschreven doorSven de Laet. It was also discussed in a broadcast of Brabant Nieuws on Thursday 11 August (fragment starts at 4:10).
Dental organization Colosseum Dental paid a ransom of about 2 million euros to end a cyber attack. Sounds intense, but it is increasingly common for companies to go overboard. This is also what Rob Mellegers of the Eindhoven company Cyber4Z sees. He regularly negotiates with hackers. "Unfortunately, it is a growth market."
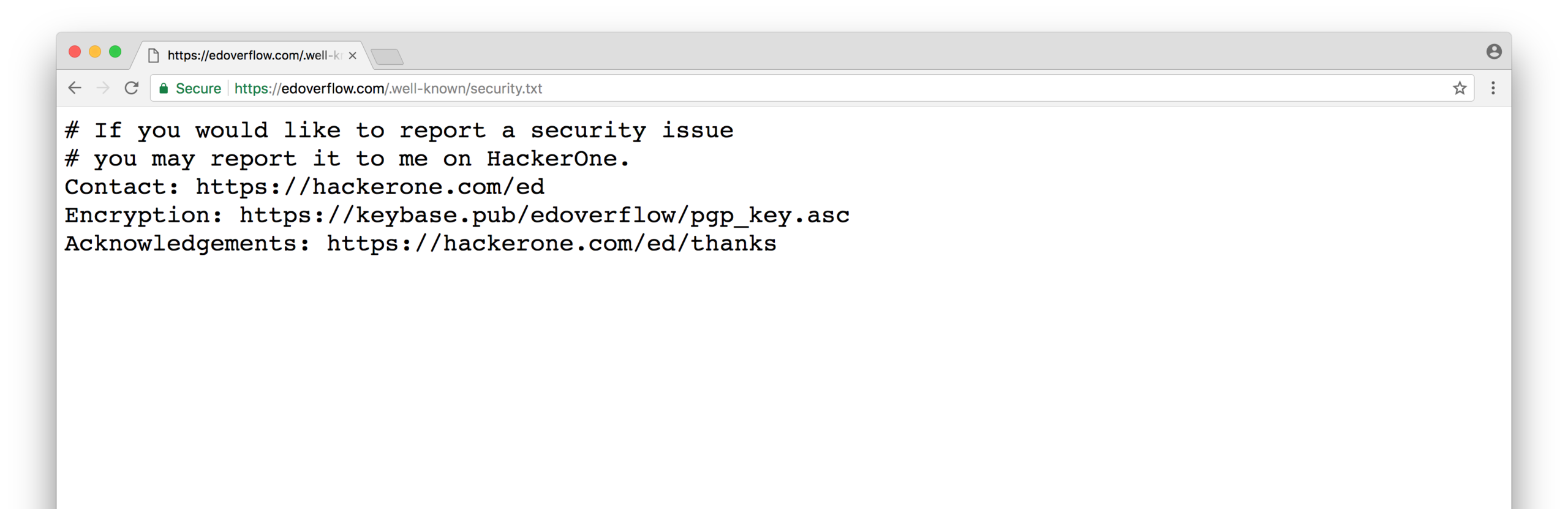
Mellegers does not know exactly who he is talking to. But he regularly has conversations with hackers, who want ransom. "Companies approach us when they are attacked. How do they know that they have been hacked? You soon find out that you can no longer use programs."
At such a moment, Mellegers and his colleagues spring into action. That communication often runs smoothly. "You will be sent a link, which will take you to a secure portal. Sometimes you can just talk to each other, as if through a kind of crypto telephone."
Mellegers' task is clear. "Make agreements with the hackers on behalf of the hacked company. Sometimes there is room for negotiation. They are very open about that. Those criminals also know exactly what they can ask of you. They have looked up your turnover for a long time, so they can also estimate whether haggling is really necessary."
But isn't it strange to chat with such a hacker? "Somehow, because you know that they have done something that is not right. But I am mainly busy limiting the damage for my client. The conversations are often very friendly. They are nice to me, I to them. It is best to make agreements, for example about paying in installments, so that you know that they actually return data."
Because that's the risk: will the hackers give that data back? "It is of course possible that they sell the data or make it public. But in general it is much more useful for them to be reliable. If they do not deliver once, everyone will know immediately. Then it makes no sense for the next hacked company to pay."
Paying is happening more and more often. "Also because the measures at companies are getting better and better. Hackers are therefore able to steal less data, which means that it also involves smaller amounts." And while ransom transfers are strongly discouraged, Mellegers can imagine paying it. "A company is the only one able to assess the impact, damage and consequences if that data ends up on the street."
Incidentally, it is not the case that companies transfer the ransom quickly to avoid negative publicity. "The moment you are hacked, you are simply obliged to report it to the Dutch Data Protection Authority."
It doesn't look like Mellegers' agenda is getting emptier any time soon. "Unfortunately, hacking is a growth market. Am I not doing my job properly? Well, you are never completely safe. It is and remains the fault of the hackers themselves."